We provide real 156-215.80 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Check-Point 156-215.80 Exam quickly & easily. The 156-215.80 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Check-Point 156-215.80 dumps pdf and vce product and material, you can easily pass the 156-215.80 exam.
Check-Point 156-215.80 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
How do you configure an alert in SmartView Monitor?
- A. An alert cannot be configured in SmartView Monitor.
- B. By choosing the Gateway, and Configure Thresholds.
- C. By right-clicking on the Gateway, and selecting Properties.
- D. By right-clicking on the Gateway, and selecting System Information.
Answer: B
NEW QUESTION 2
Which of the following is NOT an advantage to using multiple LDAP servers?
- A. You achieve a faster access time by placing LDAP servers containing the database at remote sites
- B. Information on a user is hidden, yet distributed across several servers
- C. You achieve compartmentalization by allowing a large number of users to be distributed across several servers
- D. You gain High Availability by replicating the same information on several servers
Answer: B
NEW QUESTION 3
Please choose correct command syntax to add an “emailserver1” host with IP address 10.50.23.90 using GAiA management CLI?
- A. host name myHost12 ip-address 10.50.23.90
- B. mgmt add host name ip-address 10.50.23.90
- C. add host name emailserver1 ip-address 10.50.23.90
- D. mgmt add host name emailserver1 ip-address 10.50.23.90
Answer: D
NEW QUESTION 4
While enabling the Identity Awareness blade the Identity Awareness wizard does not automatically detect the windows domain. Why does it not detect the windows domain?
- A. Security Gateways is not part of the Domain
- B. SmartConsole machine is not part of the domain
- C. SMS is not part of the domain
- D. Identity Awareness is not enabled on Global properties
Answer: B
Explanation:
To enable Identity Awareness:
Log in to SmartDashboard.
From the Network Objects tree, expand the Check Poinbtranch.
Double-click the Security Gateway on which to enable Identity Awareness.
In the Software Blades section, select Identity Awarenesosn the Network Security tab. The Identity Awareness Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers.
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
Terminal Servers - Identify users in a Terminal Server environment (originating from one IP address).
See Choosing Identity Sources.
Note - When you enable Browser-Based Authentication on a Security Gateway that is on an IP Series appliance, make sure to set the Voyager management application port to a port other than 443 or 80.
Click Next.
The Integration With Active Directory window opens.
When SmartDashboard is part of the domain, SmartDashboard suggests this domain automatically. If you select this domain, the system creates an LDAP Account Unit with alolf the domain controllers in the organization's Active Directory.
NEW QUESTION 5
In what way are SSL VPN and IPSec VPN different?
- A. SSL VPN is using HTTPS in addition to IKE, whereas IPSec VPN is clientless
- B. SSL VPN adds an extra VPN header to the packet, IPSec VPN does not
- C. IPSec VPN does not support two factor authentication, SSL VPN does support this
- D. IPSec VPN uses an additional virtual adapter, SSL VPN uses the client network adapter only
Answer: D
NEW QUESTION 6
Tom has been tasked to install Check Point R80 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
- A. One machine, but it needs to be installed using SecurePlatform for compatibility purposes.
- B. One machine
- C. Two machines
- D. Three machines
Answer: C
Explanation:
One for Security Management Server and the other one for the Security Gateway.
NEW QUESTION 7
After the initial installation the First Time Configuration Wizard should be run. Select the BEST answer.
- A. First Time Configuration Wizard can be run from the Unified SmartConsole.
- B. First Time Configuration Wizard can be run from the command line or from the WebUI.
- C. First time Configuration Wizard can only be run from the WebUI.
- D. Connection to the internet is required before running the First Time Configuration wizard.
Answer: B
Explanation:
Check Point Security Gateway and Check Point Security Management require running the First Time Configuration Wizard in order to be configured correctly. The First Time Configuration Wizard is available in Gaia Portal and also through CLI.
To invoke the First Time Configuration Wizard through CLI, run the config_system command from the Exp shell.
NEW QUESTION 8
Full synchronization between cluster members is handled by Firewall Kernel. Which port is used for this?
- A. UDP port 265
- B. TCP port 265
- C. UDP port 256
- D. TCP port 256
Answer: B
NEW QUESTION 9
Which of the following is a hash algorithm?
- A. 3DES
- B. IDEA
- C. DES
- D. MD5
Answer: D
NEW QUESTION 10
You have enabled “Full Log” as a tracking option to a security rule. However, you are still not seeing any data type information. What is the MOST likely reason?
- A. Logging has disk space issue
- B. Change logging storage options on the logging server or Security Management Server properties and install database.
- C. Data Awareness is not enabled.
- D. Identity Awareness is not enabled.
- E. Logs are arriving from Pre-R80 gateways.
Answer: A
Explanation:
The most likely reason for the logs data to stop is the low disk space on the logging device, which can be the Management Server or the Gateway Server.
NEW QUESTION 11
The security Gateway is installed on GAiA R80 The default port for the WEB User Interface is ____.
- A. TCP 18211
- B. TCP 257
- C. TCP 4433
- D. TCP 443
Answer: D
NEW QUESTION 12
Which of the following is NOT a license activation method?
- A. SmartConsole Wizard
- B. Online Activation
- C. License Activation Wizard
- D. Offline Activation
Answer: A
NEW QUESTION 13
Fill in the blanks: A Check Point software license consists of a _____ and ______.
- A. Software container; software package
- B. Software blade; software container
- C. Software package; signature
- D. Signature; software blade
Answer: B
Explanation:
Check Point's licensing is designed to be scalable and modular. To this end, Check Point offers both predefined packages as well as the ability to custom build a solution tailored to the needs of the Network Administrator. This is accomplished by the use of the following license components:
Software Blades
Container
NEW QUESTION 14
Which of the following is NOT an attribute of packer acceleration?
- A. Source address
- B. Protocol
- C. Destination port
- D. Application Awareness
Answer: D
NEW QUESTION 15
What must a Security Administrator do to comply with a management requirement to log all traffic accepted through the perimeter Security Gateway?
- A. In Global Properties > Reporting Tools check the box Enable tracking all rules (including rules marked as None in the Track column). Send these logs to a secondary log server for a complete logging histor
- B. Use your normal log server for standard logging for troubleshooting.
- C. Install the View Implicit Rules package using SmartUpdate.
- D. Define two log servers on the R77 Gateway objec
- E. Lof Implied Rules on the first log serve
- F. Enable Log Rule Base on the second log serve
- G. Use SmartReporter to merge the two log server records into the same database for HIPPA log audits.
- H. Check the Log Implied Rules Globally box on the R77 Gateway object.
Answer: A
NEW QUESTION 16
Review the following screenshot and select the BEST answer.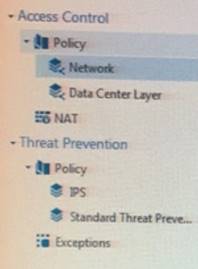
- A. Data Center Layer is an inline layer in the Access Control Policy.
- B. By default all layers are shared with all policies.
- C. If a connection is dropped in Network Layer, it will not be matched against the rules in Data Center Layer.
- D. If a connection is accepted in Network-layer, it will not be matched against the rules in Data Center Layer.
Answer: C
NEW QUESTION 17
Look at the screenshot below. What CLISH command provides this output?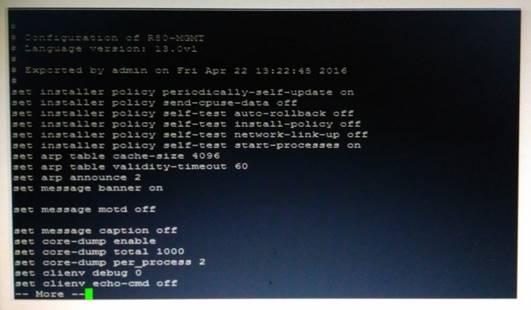
- A. show configuration all
- B. show confd configuration
- C. show confd configuration all
- D. show configuration
Answer: D
NEW QUESTION 18
What does ExternalZone represent in the presented rule?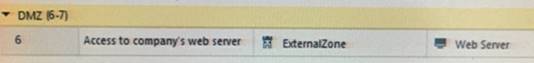
- A. The Internet.
- B. Interfaces that administrator has defined to be part of External Security Zone.
- C. External interfaces on all security gateways.
- D. External interfaces of specific gateways.
Answer: B
Explanation:
Configuring Interfaces
Configure the Security Gateway 80 interfaces in the Interfaces tab in the Security Gateway window. To configure the interfaces:
From the Devices window, double-click the Security Gateway 80.
The Security Gateway
window opens.
Select the Interfaces tab.
Select Use the following settings. The interface settings open.
Select the interface and click Edit.
The Edit window opens.
From the IP Assignment section, configure the IP address of the interface:
Select Static IP.
Enter the IP address and subnet mask for the interface.
In Security Zone, select Wireless, DMS, External, or Internal. Security zone is a type of zone, created by a bridge to easily create segments, while maintaining IP addresses and router configurations. Security zones let you choose if to enable or not the firewall between segments.
References:
NEW QUESTION 19
As you review this Security Policy, what changes could you make to accommodate Rule 4?
- A. Remove the service HTTP from the column Service in Rule 4.
- B. Modify the column VPN in Rule 2 to limit access to specific traffic.
- C. Nothing at all
- D. Modify the columns Source or Destination in Rule 4
Answer: B
NEW QUESTION 20
You installed Security Management Server on a computer using GAiA in the MegaCorp home office. You use IP address 10.1.1.1. You also installed the Security Gateway on a second GAiA computer, which you plan to ship to another Administrator at a MegaCorp hub office. What is the correct order for pushing SIC certificates to the Gateway before shipping it?
1. Run cpconfig on the Gateway, select Secure Internal Communication, enter the activation key, and reconfirm.
2. Initialize Internal Certificate Authority (ICA) on the Security Management Server.
3. Configure the Gateway object with the host name and IP addresses for the remote site.
4. Click the Communication button in the Gateway object's General screen, enter the activation key, and click Initialize and OK.
5. Install the Security Policy.
- A. 2, 3, 4, 1, 5
- B. 2, 1, 3, 4, 5
- C. 1, 3, 2, 4, 5
- D. 2, 3, 4, 5, 1
Answer: B
NEW QUESTION 21
When using LDAP as an authentication method for Identity Awareness, the query:
- A. Requires client and server side software.
- B. Prompts the user to enter credentials.
- C. Requires administrators to specifically allow LDAP traffic to and from the LDAP Server and the Security Gateway.
- D. Is transparent, requiring no client or server side software, or client intervention.
Answer: D
NEW QUESTION 22
Which pre-defined Permission Profile should be assigned to an administrator that requires full access to audit all configurations without modifying them?
- A. Auditor
- B. Read Only All
- C. Super User
- D. Full Access
Answer: B
Explanation:
To create a new permission profile:
In SmartConsole, go to Manage & Settings > Permissions and Administrators > Permission Profiles.
Click New Profile.
The New Profile window opens.
Enter a unique name for the profile.
Select a profile type:
Read/Write All - Administrators can make changes
Auditor (Read Only All) - Administrators can see information but cannot make changes
Customized - Configure custom settings
Click OK.
NEW QUESTION 23
......
Recommend!! Get the Full 156-215.80 dumps in VCE and PDF From Dumps-hub.com, Welcome to Download: https://www.dumps-hub.com/156-215.80-dumps.html (New 485 Q&As Version)