we provide Accurate Cisco 200-201 free practice questions which are the best for clearing 200-201 test, and to get certified by Cisco Understanding Cisco Cybersecurity Operations Fundamentals. The 200-201 Questions & Answers covers all the knowledge points of the real 200-201 exam. Crack your Cisco 200-201 Exam with latest dumps, guaranteed!
Cisco 200-201 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which two elements are used for profiling a network? (Choose two.)
- A. session duration
- B. total throughput
- C. running processes
- D. listening ports
- E. OS fingerprint
Answer: DE
NEW QUESTION 2
Which two pieces of information are collected from the IPv4 protocol header? (Choose two.)
- A. UDP port to which the traffic is destined
- B. TCP port from which the traffic was sourced
- C. source IP address of the packet
- D. destination IP address of the packet
- E. UDP port from which the traffic is sourced
Answer: CD
NEW QUESTION 3
Which system monitors local system operation and local network access for violations of a security policy?
- A. host-based intrusion detection
- B. systems-based sandboxing
- C. host-based firewall
- D. antivirus
Answer: C
NEW QUESTION 4
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
- A. The RST flag confirms the beginning of the TCP connection, and the ACK flag responds when the data for the payload is complete
- B. The ACK flag confirms the beginning of the TCP connection, and the RST flag responds when the data for the payload is complete
- C. The RST flag confirms the receipt of the prior segment, and the ACK flag allows for the spontaneous termination of a connection
- D. The ACK flag confirms the receipt of the prior segment, and the RST flag allows for the spontaneous termination of a connection
Answer: D
NEW QUESTION 5
Which two components reduce the attack surface on an endpoint? (Choose two.)
- A. secure boot
- B. load balancing
- C. increased audit log levels
- D. restricting USB ports
- E. full packet captures at the endpoint
Answer: AD
NEW QUESTION 6
Which two compliance frameworks require that data be encrypted when it is transmitted over a public network?
(Choose two.)
- A. PCI
- B. GLBA
- C. HIPAA
- D. SOX
- E. COBIT
Answer: AC
NEW QUESTION 7
Which artifact is used to uniquely identify a detected file?
- A. file timestamp
- B. file extension
- C. file size
- D. file hash
Answer: D
NEW QUESTION 8
Refer to the exhibit.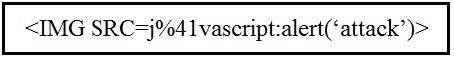
Which kind of attack method is depicted in this string?
- A. cross-site scripting
- B. man-in-the-middle
- C. SQL injection
- D. denial of service
Answer: A
NEW QUESTION 9
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
- A. syslog messages
- B. full packet capture
- C. NetFlow
- D. firewall event logs
Answer: C
NEW QUESTION 10
What is an attack surface as compared to a vulnerability?
- A. any potential danger to an asset
- B. the sum of all paths for data into and out of the application
- C. an exploitable weakness in a system or its design
- D. the individuals who perform an attack
Answer: B
NEW QUESTION 11
Drag and drop the security concept on the left onto the example of that concept on the right.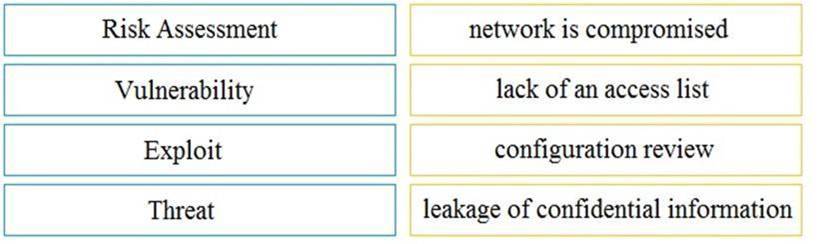
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 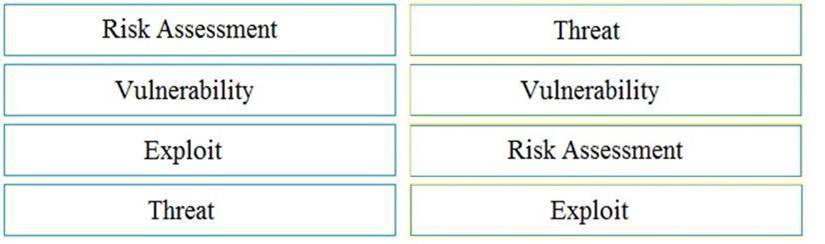
NEW QUESTION 12
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
- A. decision making
- B. rapid response
- C. data mining
- D. due diligence
Answer: A
NEW QUESTION 13
Refer to the exhibit.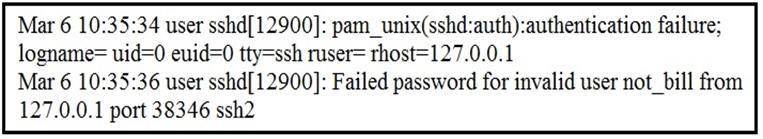
In which Linux log file is this output found?
- A. /var/log/authorization.log
- B. /var/log/dmesg
- C. var/log/var.log
- D. /var/log/auth.log
Answer: D
NEW QUESTION 14
Which NIST IR category stakeholder is responsible for coordinating incident response among various business units, minimizing damage, and reporting to regulatory agencies?
- A. CSIRT
- B. PSIRT
- C. public affairs
- D. management
Answer: D
NEW QUESTION 15
What is the difference between an attack vector and attack surface?
- A. An attack surface identifies vulnerabilities that require user input or validation; and an attack vectoridentifies vulnerabilities that are independent of user actions.
- B. An attack vector identifies components that can be exploited; and an attack surface identifies the potential path an attack can take to penetrate the network.
- C. An attack surface recognizes which network parts are vulnerable to an attack; and an attack vector identifies which attacks are possible with these vulnerabilities.
- D. An attack vector identifies the potential outcomes of an attack; and an attack surface launches an attack using several methods against the identified vulnerabilities.
Answer: C
NEW QUESTION 16
What is the practice of giving an employee access to only the resources needed to accomplish their job?
- A. principle of least privilege
- B. organizational separation
- C. separation of duties
- D. need to know principle
Answer: A
NEW QUESTION 17
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
- A. examination
- B. investigation
- C. collection
- D. reporting
Answer: C
NEW QUESTION 18
What do the Security Intelligence Events within the FMC allow an administrator to do?
- A. See if a host is connecting to a known-bad domain.
- B. Check for host-to-server traffic within your network.
- C. View any malicious files that a host has downloaded.
- D. Verify host-to-host traffic within your network.
Answer: A
NEW QUESTION 19
Which regular expression matches "color" and "colour"?
- A. colo?ur
- B. col[08]+our
- C. colou?r
- D. col[09]+our
Answer: C
NEW QUESTION 20
Which metric is used to capture the level of access needed to launch a successful attack?
- A. privileges required
- B. user interaction
- C. attack complexity
- D. attack vector
Answer: A
NEW QUESTION 21
......
P.S. Dumpscollection.com now are offering 100% pass ensure 200-201 dumps! All 200-201 exam questions have been updated with correct answers: https://www.dumpscollection.net/dumps/200-201/ (98 New Questions)