AZ-102 Exam Questions are updated and AZ-102 Exam Questions are verified by experts. Once you have completely prepared with our AZ-102 Free Practice Questions you will be ready for the real AZ-102 exam without a problem. We have AZ-102 Exam Dumps. PASSED AZ-102 Free Practice Questions First attempt! Here What I Did.
Free demo questions for Microsoft AZ-102 Exam Dumps Below:
NEW QUESTION 1
SIMULATION
Click to expand each objective. To connect to the Azure portal, type https://portal.azure.com in the browser address bar.
When you are finished performing all the tasks, click the ‘Next’ button.
Note that you cannot return to the lab once you click the ‘Next’ button. Scoring occur in the background while you complete the rest of the exam.
Overview
The following section of the exam is a lab. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design. Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
To start the lab
You may start the lab by clicking the Next button.
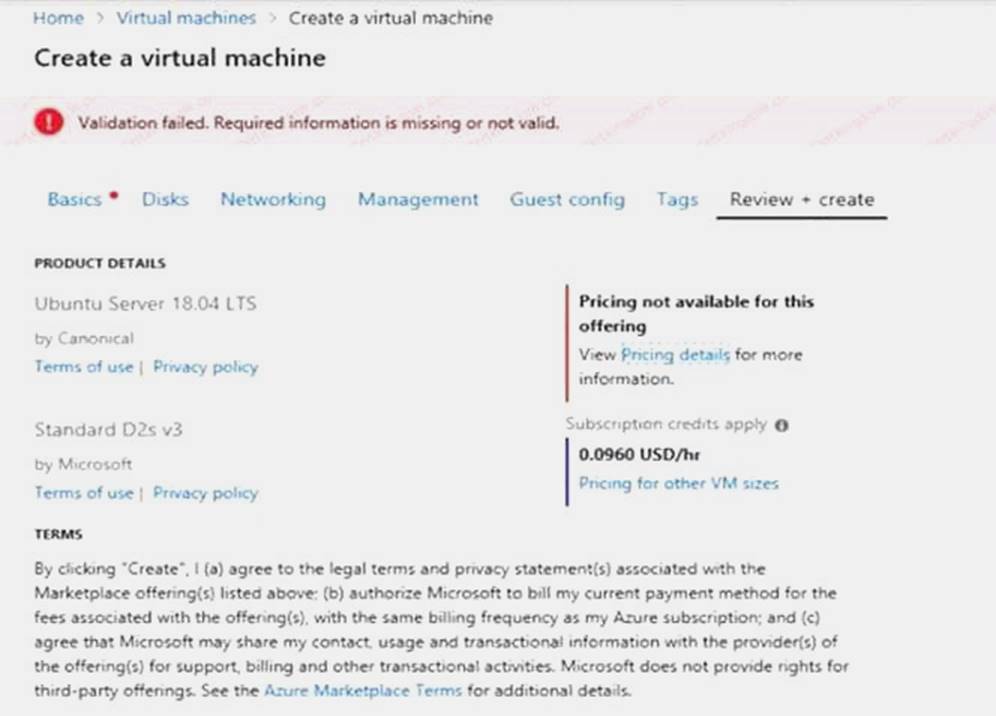
You need to deploy two Azure virtual machines named VM1003a and VM1003b based on the Ubuntu Server 17.10 image. The deployment must meet the following requirements:
Provide a Service Level Agreement (SLA) of 99.95 percent availability. Use managed disks.
What should you do from the Azure portal?
Answer:
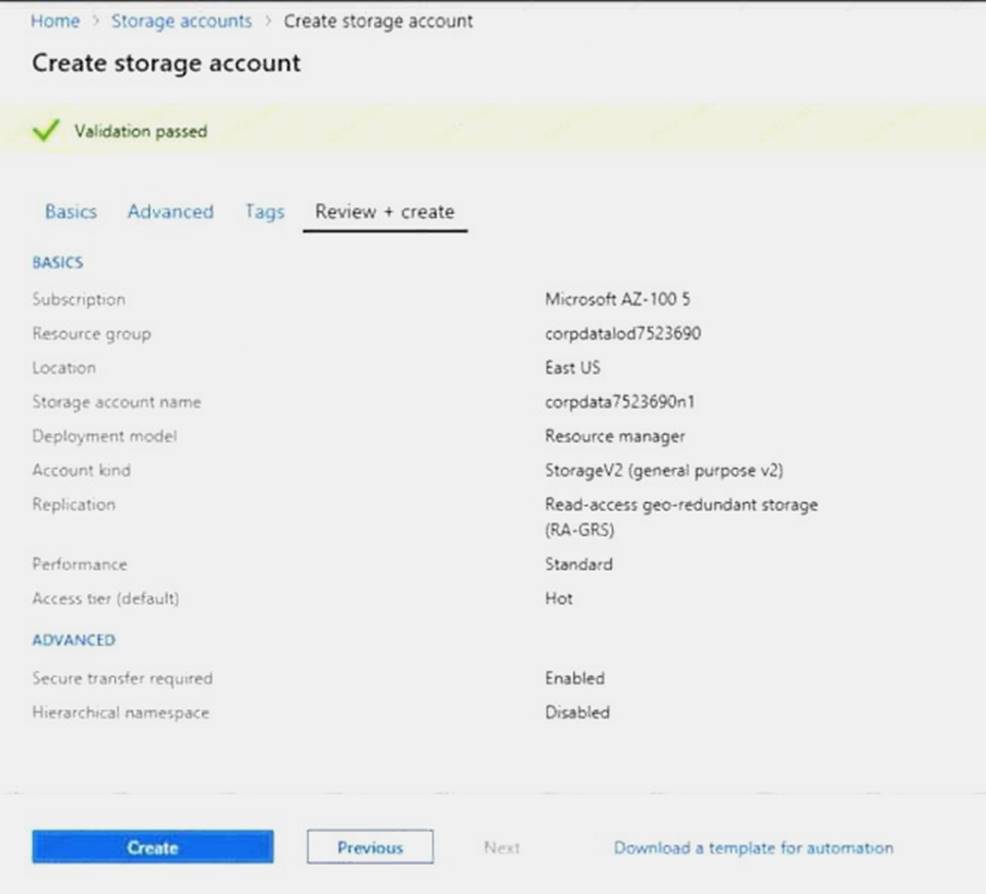
Explanation: 1. Open the Azure portal.
2. On the left menu, select All resources. You can sort the resources by Type to easily find your images.
3. Select the image you want to use from the list. The image Overview page opens.
4. Select Create VM from the menu.
5. Enter the virtual machine information.
Select VM1003a as the name for the first Virtual machine.
The user name and password entered here will be used to log in to the virtual machine. When complete, select OK. You can create the new VM in an existing resource group, or choose Create new to create a new resource group to store the VM.
6. Select a size for the VM. To see more sizes, select View all or change the Supported disk type filter.
7. Under Settings, make changes as necessary and select OK.
8. On the summary page, you should see your image name listed as a Private image. Select Ok to start the virtual machine deployment.
Repeat the procedure for the second VM and name it VM1003b.
References: https://docs.microsoft.com/en-us/azure/virtual-machines/windows/create-vmgeneralized- managed
NEW QUESTION 2
DRAG DROP
You have an Azure subscription that is used by four departments in your company. The subscription contains 10 resource groups. Each department uses resources in several resource groups.
You need to send a report to the finance department. The report must detail the costs for each department. Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.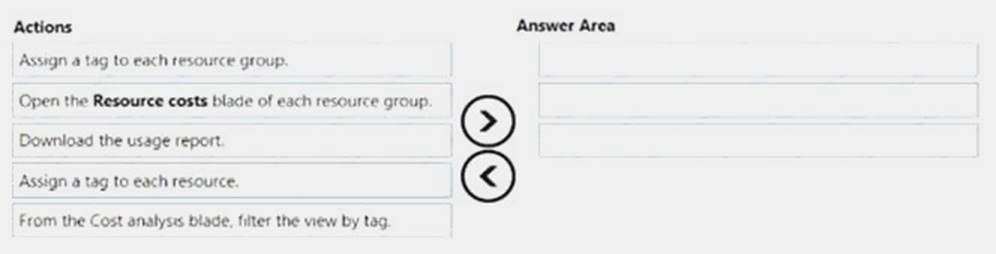
Answer:
Explanation: Box 1: Assign a tag to each resource.
You apply tags to your Azure resources giving metadata to logically organize them into a taxonomy. After you apply tags, you can retrieve all the resources in your subscription with that tag name and value. Each resource or resource group can have a maximum of 15 tag name/value pairs. Tags applied to the resource group are not inherited by the resources in that resource group.
Box 2: From the Cost analysis blade, filter the view by tag
After you get your services running, regularly check how much they're costing you. You can see the current spend and burn rate in Azure portal.
Visit the Subscriptions blade in Azure portal and select a subscription. You should see the cost breakdown and burn rate in the popup blade.
Click Cost analysis in the list to the left to see the cost breakdown by resource. Wait 24 hours after you add a service for the data to populate.
You can filter by different properties like tags, resource group, and timespan. Click Apply to confirm the filters and Download if you want to export the view to a Comma-Separated Values (.csv) file. Box 3: Download the usage report
References:
https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-using-tags https://docs.microsoft.com/en-us/azure/billing/billing-getting-started
NEW QUESTION 3
You have an Azure subscription.
You plan to use Azure Resource Manager templates to deploy 50 Azure virtual machines that will be part of the same availability set.
You need to ensure that as many virtual machines as possible are available if the fabric fails or during servicing.
How should you configure the template? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.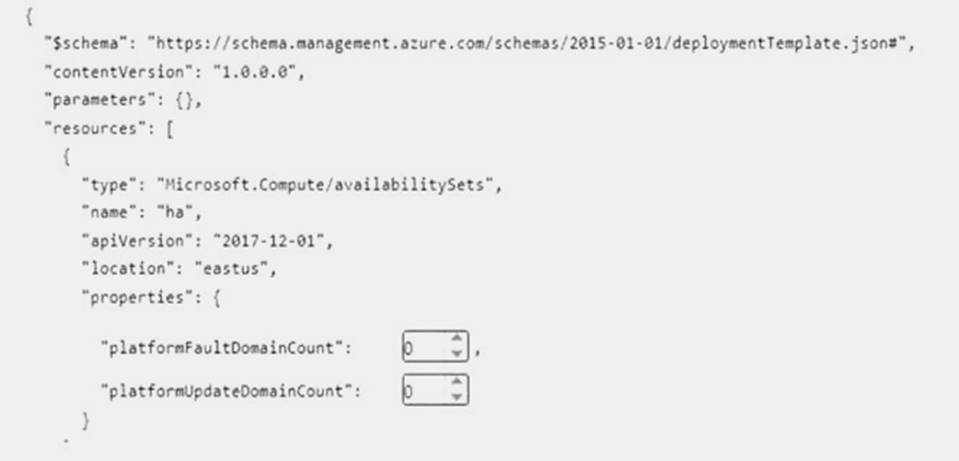
Select two alternatives below.
- A. platformFaultDomainCount: 0
- B. platformFaultDomainCount: 1
- C. platformFaultDomainCount: 2
- D. platformFaultDomainCount: 3
- E. platformFaultDomainCount: 4
- F. platformUpdateDomainCount: 10
- G. platformUpdateDomainCount: 20
- H. platformUpdateDomainCount: 25
- I. platformUpdateDomainCount: 30
- J. platformUpdateDomainCount: 40
- K. platformUpdateDomainCount: 50
Answer: CG
Explanation: Use two fault domains.
2 or 3 is max, depending on which region you are in. Use 20 for platformUpdateDomainCount
Increasing the update domain (platformUpdateDomainCount) helps with capacity and availability planning when the platform reboots nodes. A higher number for the pool (20 is max) means that fewer of their nodes in any given availability set would be rebooted at once.
References:
https://www.itprotoday.com/microsoft-azure/check-if-azure-region-supports-2-or-3-fault-domainsmanaged- disks
https://github.com/Azure/acs-engine/issues/1030
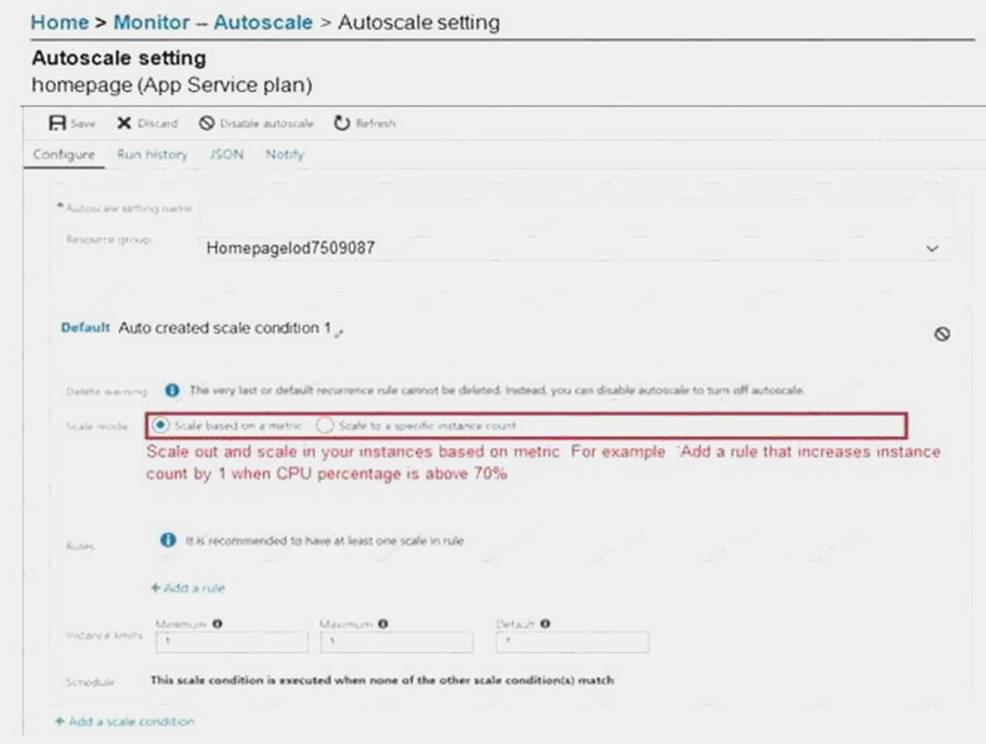
NEW QUESTION 4
You have an Azure Logic App named App1. App1 provides a response when an HTTP POST request or an HTTP GET request is received.
During peak periods, App1 is expected to receive up to 200,000 requests in a five-minute period. You need to ensure that App1 can handle the expected load.
What should you configure?
- A. Access keys
- B. Access control (1AM)
- C. API connections
- D. Workflow settings
Answer: D
Explanation: Here are the limits for a single logic app definition: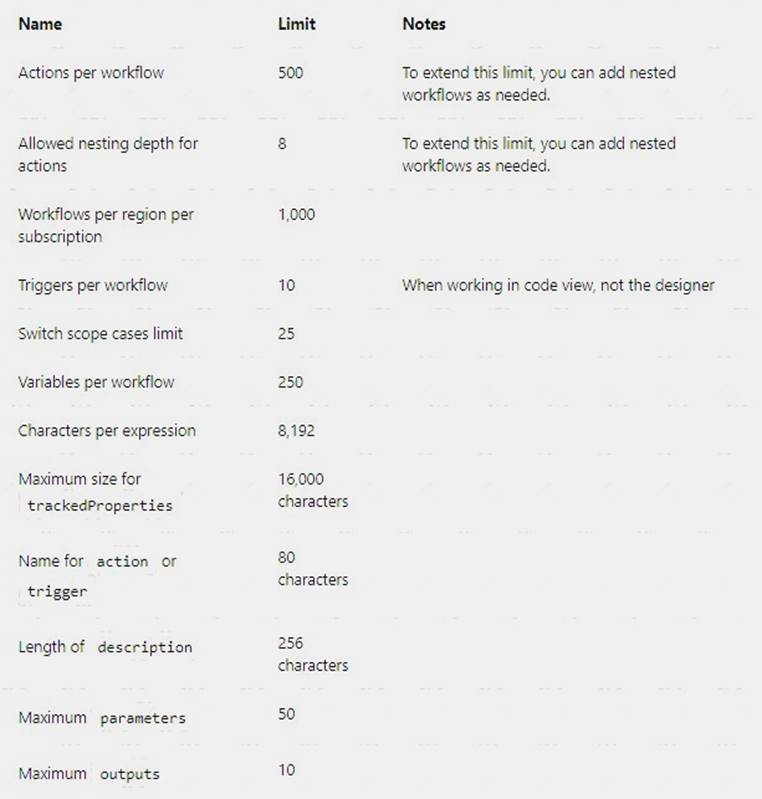
References:
https://docs.microsoft.com/en-us/azure/logic-apps/logic-apps-limits-and-config
NEW QUESTION 5
You have an Azure subscription that contains the resources in the following table.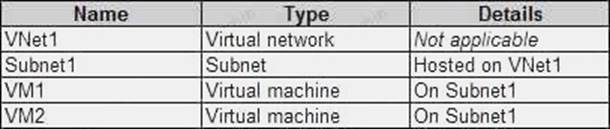
VM1 and VM2 are deployed from the same template and host line-of-business applications accessed by using Remote Desktop. You configure the network security group (NSG) shown in the exhibit. (Click the Exhibit button.)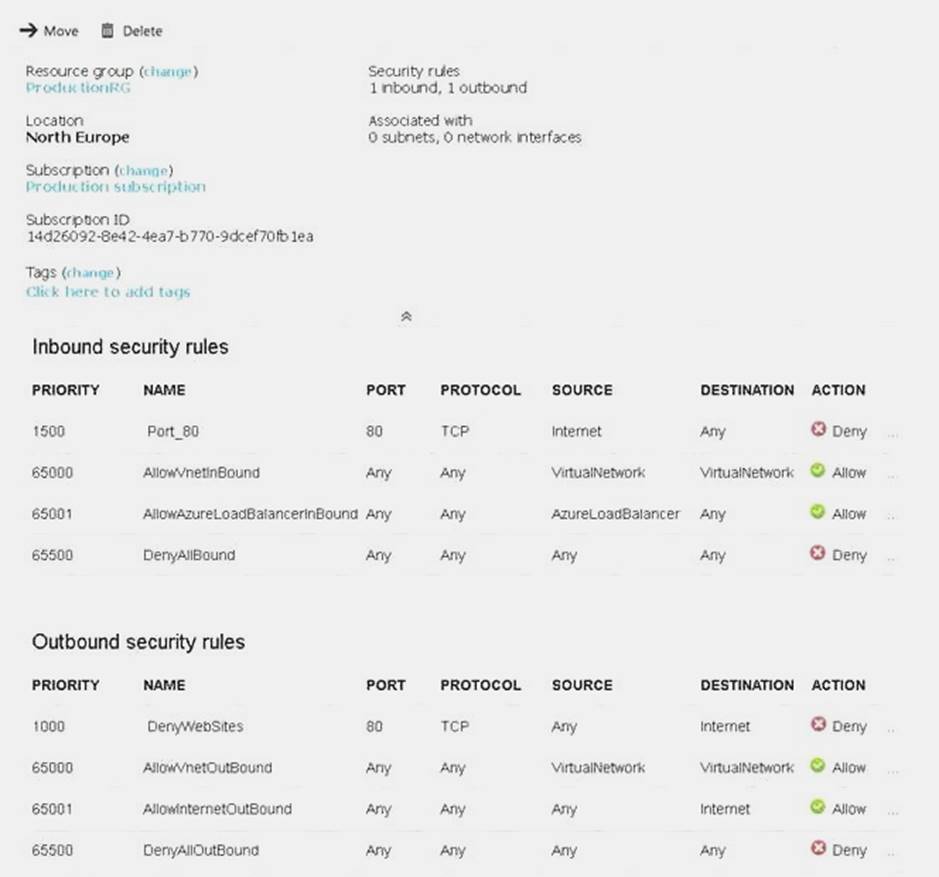
You need to prevent users of VM1 and VM2 from accessing websites on the Internet. What should you do?
- A. Associate the NSG to Subnet1.
- B. Disassociate the NSG from a network interface.
- C. Change the DenyWebSites outbound security rule.
- D. Change the Port_80 inbound security rul
Answer: A
Explanation: You can associate or dissociate a network security group from a network interface or subnet.
The NSG has the appropriate rule to block users from accessing the Internet. We just need to associate it with Subnet1.
References: https://docs.microsoft.com/en-us/azure/virtual-network/manage-network-securitygroup
NEW QUESTION 6
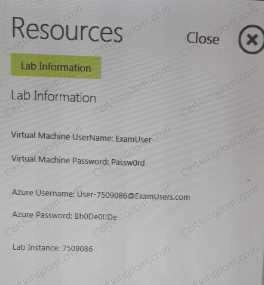
You plan to grant the member of a new Azure AD group named crop 75099086 the right to delegate administrative access to any resource in the resource group named 7509086.
You need to create the Azure AD group and then to assign the correct to e to the group. The solution must use the principle of least privilege and minimize the number of role assignments.
What should you do from the Azure portal?
Answer:
Explanation: Step 1:
Click Resource groups from the menu of services to access the Resource Groups blade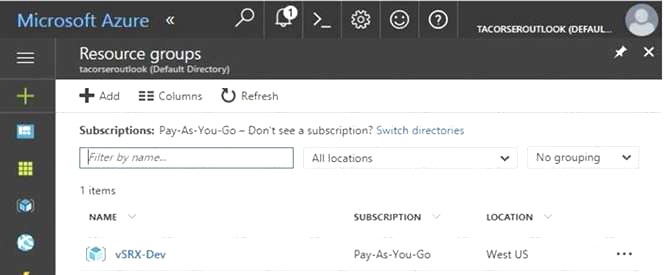
Step 2:
Click Add (+) to create a new resource group. The Create Resource Group blade appears. Enter corp7509086 as the Resource group name, and click the Create button.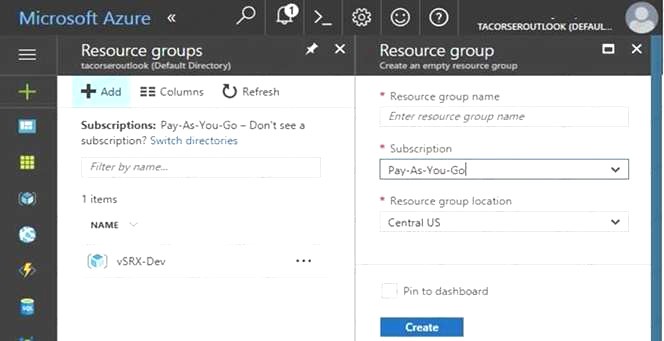
Step 3: Select Create.
Your group is created and ready for you to add members. Now we need to assign a role to this resource group scope. Step 4:
Choose the newly created Resource group, and Access control (IAM) to see the current list of role assignments at the resource group scope. Click +Add to open the Add permissions pane.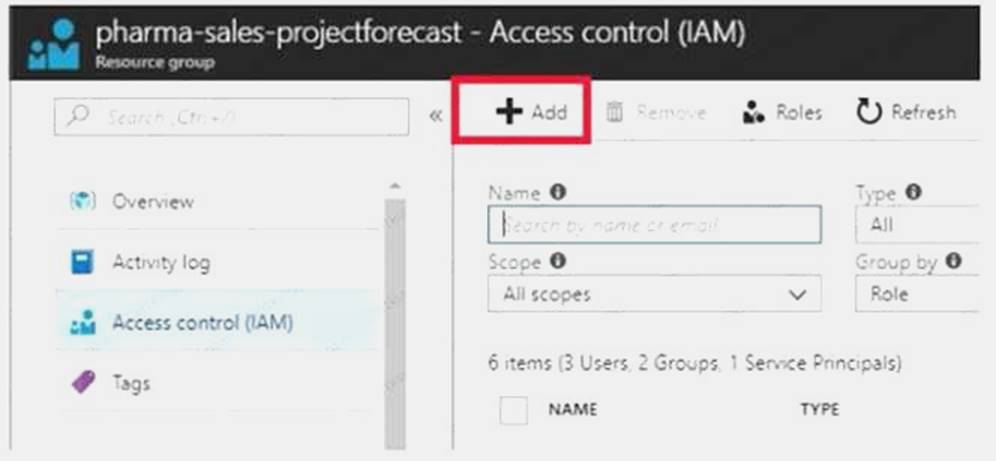
Step 5:
In the Role drop-down list, select a role Delegate administration, and select Assign access to: resource group corp7509086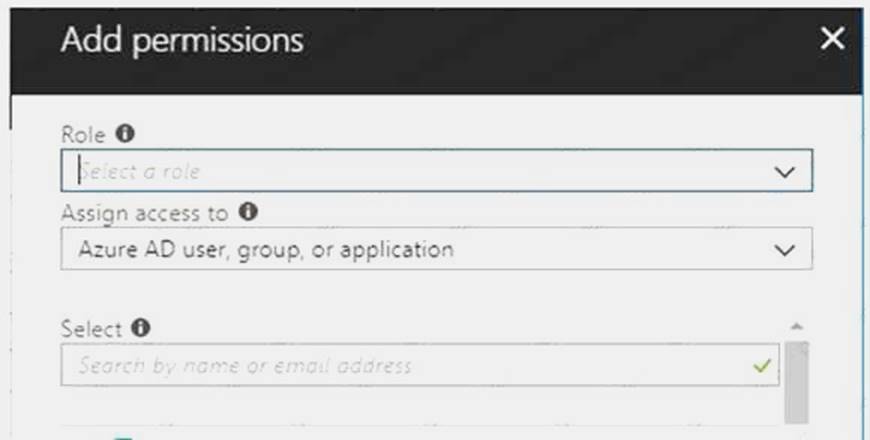
References:
https://docs.microsoft.com/en-us/azure/role-based-access-control/role-assignments-portal https://www.juniper.net/documentation/en_US/vsrx/topics/task/multi-task/security-vsrx-azuremarketplace- resource-group.html
Case Study: 11
Mix Questions Set E (Security Identities)
NEW QUESTION 7
Your company has an Azure subscription named Subscription1.
The company also has two on-premises servers named Server1 and Server2 that run Windows Server 2021. Server1 is configured as a DNS server that has a primary DNS zone named adatum.com. Adatum.com contains 1,000 DNS records.
You manage Server1 and Subscription1 from Server2. Server2 has the following tools installed: The DNS Manager console
Azure PowerShell Azure CLI 2.0
You need to move the adatum.com zone to Subscription1. The solution must minimize administrative effort.
What should you use?
- A. Azure PowerShell
- B. Azure CLI
- C. the Azure portal
- D. the DNS Manager console
Answer: B
Explanation: Azure DNS supports importing and exporting zone files by using the Azure command-line interface (CLI). Zone file import is not currently supported via Azure PowerShell or the Azure portal. References: https://docs.microsoft.com/en-us/azure/dns/dns-import-export
NEW QUESTION 8
Note: This question is part of a series of Questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more
than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure virtual machine named VM1. VM1 was deployed by using a custom Azure Resource Manager template named ARM1.json.
You receive a notification that VM1 will be affected by maintenance. You need to move VM1 to a different host immediately.
Solution: From the Overview blade, you move the virtual machine to a different resource group. Does this meet the goal?
- A. Yes
- B. No
Answer: B
NEW QUESTION 9
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure web app named Appl. App1 runs in an Azure App Service plan named Plan1. Plan1 is associated to the Free pricing tier.
You discover that App1 stops each day after running continuously for 60 minutes. You need to ensure that App1 can run continuously for the entire day.
Solution: You change the pricing tier of Plan1 to Basic. Does this meet the goal?
- A. Yes
- B. No
Answer: A
Explanation: The Free Tier provides 60 CPU minutes / day. This explains why App1 is stops. The Basic tier has no such cap.
References:
https://azure.microsoft.com/en-us/pricing/details/app-service/windows/
NEW QUESTION 10
You need to prepare the environment to meet the authentication requirements.
Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A. Allow inbound TCP port 8080 to the domain controllers in the Miami office.
- B. Add http://autogon.microsoftazuread-sso.com to the intranet zone of each client computer in the Miamioffice.
- C. Join the client computers in the Miami office to Azure AD.
- D. Install the Active Directory Federation Services (AD FS) role on a domain controller in the Miami office.
- E. Install Azure AD Connect on a server in the Miami office and enable Pass-through Authenticatio
Answer: BE
Explanation: B: You can gradually roll out Seamless SSO to your users. You start by adding the following Azure AD URL to all or selected users' Intranet zone settings by using Group Policy in Active Directory: https://autologon.microsoftazuread-sso.com
E: Seamless SSO works with any method of cloud authentication - Password Hash Synchronization or Pass-through Authentication, and can be enabled via Azure AD Connect.
References:
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-sso-quick-start
Case Study: 2
Contoso Ltd Overview
Contoso, Ltd. is a manufacturing company that has offices worldwide. Contoso works with partner organizations to bring products to market.
Contoso products are manufactured by using blueprint files that the company authors and maintains. Existing Environment
Currently, Contoso uses multiple types of servers for business operations, including the following:
? File servers
? Domain controllers
? Microsoft SQL Server servers
Your network contains an Active Directory forest named contoso.com. All servers and client computers are joined to Active Directory.
You have a public-facing application named App1. App1 is comprised of the following three tiers:
? A SQL database
? A web front end
? A processing middle tier
Each tier is comprised of five virtual machines. Users access the web front end by using HTTPS only. Requirements
Planned Changes
Contoso plans to implement the following changes to the infrastructure: Move all the tiers of App1 to Azure.
Move the existing product blueprint files to Azure Blob storage.
Create a hybrid directory to support an upcoming Microsoft Office 365 migration project. Technical Requirements
Contoso must meet the following technical requirements: Move all the virtual machines for App1 to Azure. Minimize the number of open ports between the App1 tiers.
Ensure that all the virtual machines for App1 are protected by backups. Copy the blueprint files to Azure over the Internet.
Ensure that the blueprint files are stored in the archive storage tier. Ensure that partner access to the blueprint files is secured and temporary.
Prevent user passwords or hashes of passwords from being stored in Azure. Use unmanaged standard storage for the hard disks of the virtual machines.
Ensure that when users join devices to Azure Active Directory (Azure AD), the users use a mobile phone to verify their identity.
Minimize administrative effort whenever possible. User Requirements
Contoso identifies the following requirements for users:
Ensure that only users who are part of a group named Pilot can join devices to Azure AD. Designate a new user named Admin1 as the service administrator of the Azure subscription. Ensure that a new user named User3 can create network objects for the Azure subscription.
NEW QUESTION 11
HOT SPOT
You have an Azure subscription named Subscription1. Subscription1 contains the resources in the following table.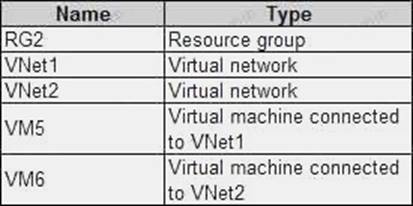
In Azure, you create a private DNS zone named adatum.com. You set the registration virtual network to VNet2. The adatum.com zone is configured as shown in the following exhibit.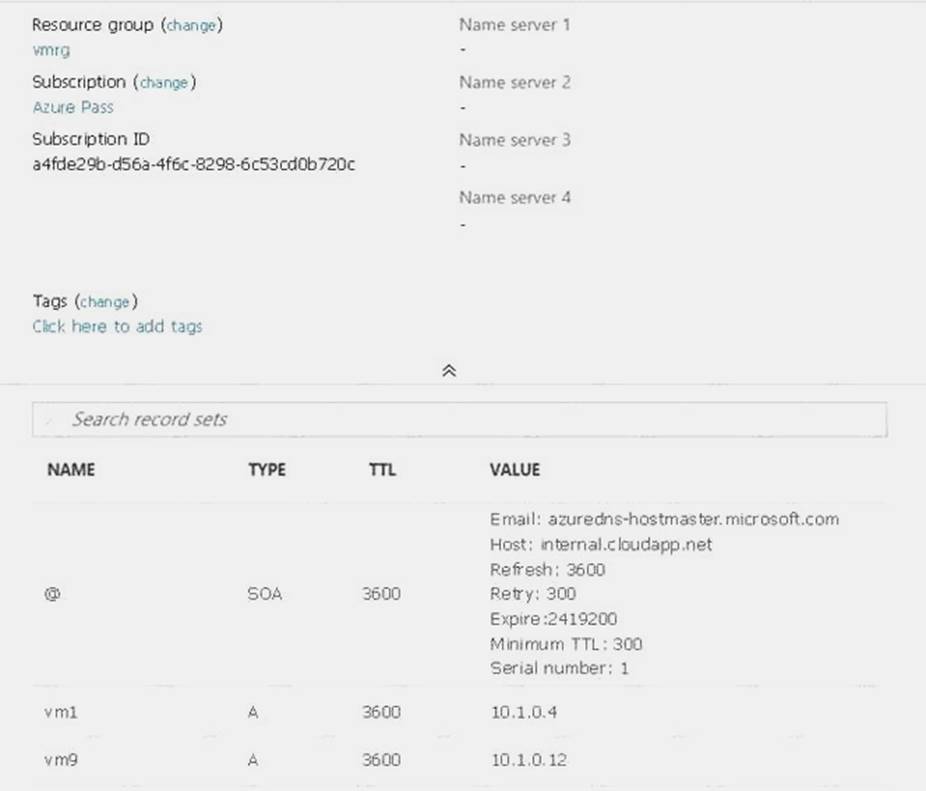
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Answer:
Explanation: Box 1: No
Azure DNS provides automatic registration of virtual machines from a single virtual network that's linked to a private zone as a registration virtual network. VM5 does not belong to the registration virtual network though.
Box 2: No
Forward DNS resolution is supported across virtual networks that are linked to the private zone as resolution virtual networks. VM5 does belong to a resolution virtual network.
Box 3: Yes
VM6 belongs to registration virtual network, and an A (Host) record exists for VM9 in the DNS zone. By default, registration virtual networks also act as resolution virtual networks, in the sense that DNS resolution against the zone works from any of the virtual machines within the registration virtual network.
References: https://docs.microsoft.com/en-us/azure/dns/private-dns-overview
NEW QUESTION 12
You have a Microsoft SQL Server Always On availability group on Azure virtual machines. You need to configure an Azure internal load balancer as a listener for the availability group. What should you do?
- A. Enable Floating IP.
- B. Set Session persistence to Client IP and protocol.
- C. Set Session persistence to Client IP.
- D. Create an HTTP health probe on port 1433.
Answer: A
Explanation: Incorrect Answers:
D: The Health probe is created with the TCP protocol, not with the HTTP protocol. References:
https://docs.microsoft.com/en-us/azure/virtual-machines/windows/sql/virtual-machines-windowsportal- sql-alwayson-int-listener
Case Study: 6
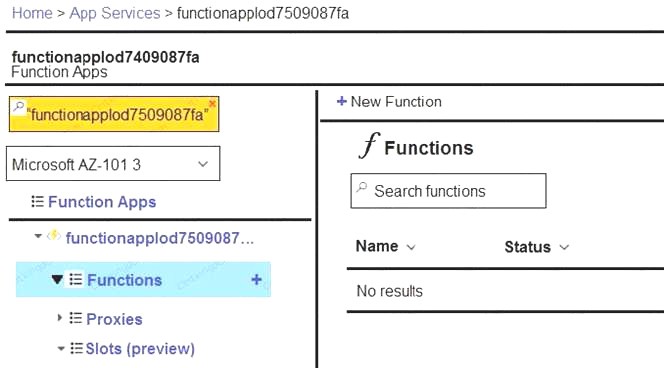
Lab 1 SIMULATION
The following section of the exam is a lab. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please, note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
To start the lab
You may start lab by clicking the Next button Tasks
Click to expand each objective
To connect to the Azure portal, type https:/portal.azure.com in the browser address bar. Instructions
Performance Based Lab
This type of question asks you to perform tasks in a virtual environment.
The screen for this type of question includes a virtual machine window and a tasks pane.
The window is a remotely connected live environment where you perform tasks on real software and applications.
On the right is a Tasks pane that lists the tasks you need to perform in the lab. Each task can be expanded or collapsed using the “+” or “-” symbols. A checkbox is provided for each task. This is provided for convenience, so you can mark each task as you complete it.
Tasks
Click to expand each objective
-Configure servers
Add the “Print and Document Services” role to server LON-SVR1, installing any required management features and enabling both Print and LPD Services.
+Configure file and share access
When you are finished performing all the tasks, click the ‘Next’ button.
Note that you cannot return to the lab once you click the ‘Next’ button. Scoring occur in the background while you complete the rest of the exam.
Comments
Once the exam completes, the comment period will begin and you will have the opportunity to provide comments to Microsoft about the exam questions. To launch the comment period, click the “Finish” and then “Comment” buttions. To skip the comment period and the exam, click Exit.
You can navigate to a question from the Review screen to provide a comment. Please, see the Review Screen tab in the Review Screen help Menu (which can be accessed from the Review Screen) for details on accessing questions from the Review Screen.
To comment on a question, navigate to that question and click the Give Feedback icon. When you have entered your comment in the comment window, click Submit to close the window. To navigate to the Review screen again, click the Review button. You may navigate through all questions using the Next and Previous buttions. To skip commenting, go to the Review Screen by selecting the Review Screen button in the upper left-hand corner and from the Review Screen, select “Finished”.
Controls Available
For any question, one or more of the following controls might be available.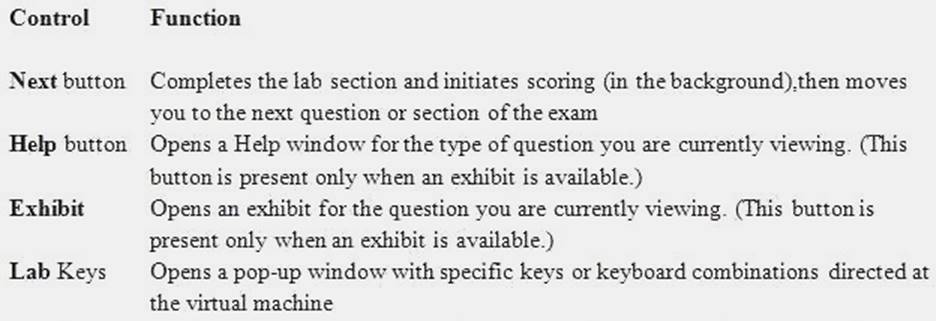
Keyboard Shortcuts Available
Exam features may be accessed using keyboard shortcuts. The following table describes the keyboard shortcuts that are available during this exam.
Some keyboard shortcuts require that you press two or more keys at the same time. These keys are separated by a plus sign (+) in the table below.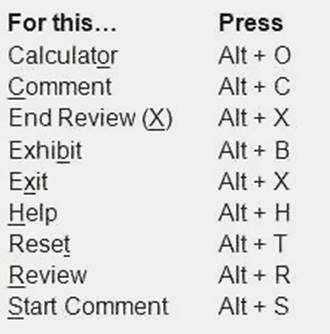
NEW QUESTION 13
HOT SPOT
You need to identify the storage requirements for Contoso.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.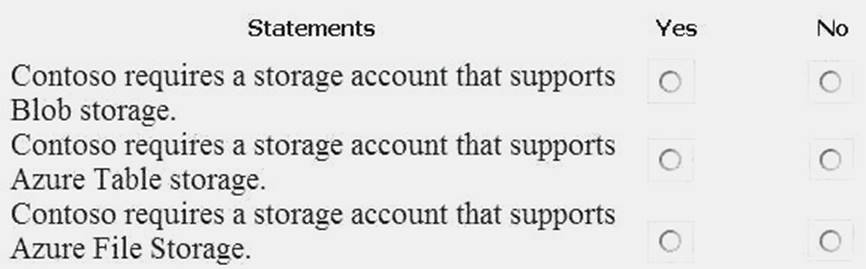
Answer:
Explanation:
Box 1: Yes
Contoso is moving the existing product blueprint files to Azure Blob storage.
Use unmanaged standard storage for the hard disks of the virtual machines. We use Page Blobs for these.
Box 2: No
Box 3: No
Case Study: 3
Mix Questions
NEW QUESTION 14
You configure Azure AD Connect for Azure Active Directory Seamless Single Sign-On (Azure AD Seamless SSO) for an on-premises network. Users report that when they attempt to access myapps.microsoft.com, they are prompted multiple times to sign in and are forced to use an account name that ends with onmicrosoft.com.
You discover that there is a UPN mismatch between Azure AD and the on-premises Active Directory. You need to ensure that the users can use single-sign on (SSO) to access Azure resources.
What should you do first?
- A. From the on-premises network, deploy Active Directory Federation Services (AD FS).
- B. From Azure AD, add and verify a custom domain name.
- C. From the on-premises network, request a new certificate that contains the Active Directory domain name.
- D. From the server that runs Azure AD Connect, modify the filtering option
Answer: B
Explanation: Azure AD Connect lists the UPN suffixes that are defined for the domains and tries to match them
with a custom domain in Azure AD. Then it helps you with the appropriate action that needs to be taken. The Azure AD sign-in page lists the UPN suffixes that are defined for on-premises Active Directory and displays the corresponding status against each suffix. The status values can be one of the following:
State: Verified Azure AD Connect found a matching verified domain in Azure AD. All users for this domain can sign in by using their on-premises credentials.
State: Not verified Azure AD Connect found a matching custom domain in Azure AD, but it isn't verified. The UPN suffix of the users of this domain will be changed to the default .onmicrosoft.com suffix after synchronization if the domain isn't verified.
Action Required: Verify the custom domain in Azure AD.
References: https://docs.microsoft.com/en-us/azure/active-directory/hybrid/plan-connect-userQuestions& Answers PDF P-80 signin
NEW QUESTION 15
You are troubleshooting a performance issue for an Azure Application Gateway. You need to compare the total requests to the failed requests during the past six hours. What should you use?
- A. Metrics in Application Gateway
- B. Diagnostics logs in Application Gateway
- C. NSG flow logs in Azure Network Watcher
- D. Connection monitor in Azure Network Watcher
Answer: A
Explanation: Application Gateway currently has seven metrics to view performance counters.
Metrics are a feature for certain Azure resources where you can view performance counters in the portal. For Application Gateway, the following metrics are available: Total Requests
Failed Requests Current Connections Healthy Host Count Response Status Throughput Unhealthy Host count
You can filter on a per backend pool basis to show healthy/unhealthy hosts in a specific backend pool References: https://docs.microsoft.com/en-us/azure/application-gateway/applicationgatewaydiagnostics# Metrics
NEW QUESTION 16
You sign up for Azure Active Directory (Azure AD) Premium.
You need to add a user named admin1@contoso.com as an administrator on all the computers that will be joined to the Azure AD domain.
What should you configure in Azure AD?
- A. Device settings from the Devices blade.
- B. General settings from the Groups blade.
- C. User settings from the Users blade.
- D. Providers from the MFA Server blade.
Answer: C
Explanation: When you connect a Windows device with Azure AD using an Azure AD join, Azure AD adds the following security principles to the local administrators group on the device:
The Azure AD global administrator role The Azure AD device administrator role
The user performing the Azure AD join In the Azure portal, you can manage the device administrator role on the Devices page. To open the Devices
page: 1. Sign in to your Azure portal as a global administrator or device administrator.
2. On the left navbar, click Azure Active Directory.
3. In the Manage section, click Devices.
4. On the Devices page, click Device settings.
5. To modify the device administrator role, configure Additional local administrators on Azure AD joined
devices.
References: https://docs.microsoft.com/en-us/azure/active-directory/devices/assign-local-admin
NEW QUESTION 17
You have an Azure subscription that contains a policy-based virtual network gateway named GW1 and a virtual network named VNet1. You need to ensure that you can configure a point-to-site connection from VNet1 to an on-premises computer. Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. Reset GW1.
- B. Add a service endpoint to VNet1.
- C. Add a connection to GW1.
- D. Add a public IP address space to VNet1.
- E. Delete GWL
- F. Create a route-based virtual network gatewa
Answer: EF
Explanation: E: Policy-based VPN devices use the combinations of prefixes from both networks to define how traffic is encrypted/decrypted through IPsec tunnels. It is typically built on firewall devices that perform packet filtering. IPsec tunnel encryption and decryption are added to the packet filtering and processing engine.
F: A VPN gateway is used when creating a VPN connection to your on-premises network.
Route-based VPN devices use any-to-any (wildcard) traffic selectors, and let routing/forwarding tables direct traffic to different IPsec tunnels. It is typically built on router platforms where each IPsec tunnel is modeled as a network interface or VTI (virtual tunnel interface).
Incorrect Answers:
D: Point-to-Site connections do not require a VPN device or a public-facing IP address. References:
https://docs.microsoft.com/en-us/azure/vpn-gateway/create-routebased-vpn-gateway-portal https://docs.microsoft.com/en-us/azure/vpn-gateway/vpn-gateway-connect-multiple-policybasedrm- ps
Case Study: 10
Lab 2 Overview
This is a lab or performance-based testing (PBT) section.
The following section of the exam is a lab. In this section, you will perform a set of tasks m a live environment. While most liable to you as it would be m a live environment, some functionality (e g, copy and paste, ability to having sites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn't matter how you accomplish the lab9s0 and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab. you will NOT be able to return to the tab.
To connect to Azure portal, type https://portal.azure.com in te browser address bar.
NEW QUESTION 18
You have an Azure Active Directory (Azure AD) tenant.
All administrators must enter a verification code to access the Azure portal.
You need to ensure that the administrators can access the Azure portal only from your on-premises network. What should you configure?
- A. the multi-factor authentication service settings
- B. an Azure AD Identity Protection user risk policy
- C. the default for all the roles in Azure AD Privileged Identity Management
- D. an Azure AD Identity Protection sign-in risk policy
Answer: A
NEW QUESTION 19
DRAG DROP
You have an Azure Active Directory (Azure AD) tenant that has the initial domain name. You have a domain name of contoso.com registered at a third-party registrar.
You need to ensure that you can create Azure AD users that have names containing a suffix of
@contoso.com.
Which three actions should you perform in sequence? To answer, move the appropriate cmdlets from the list of cmdlets to the answer area and arrange them in the correct order.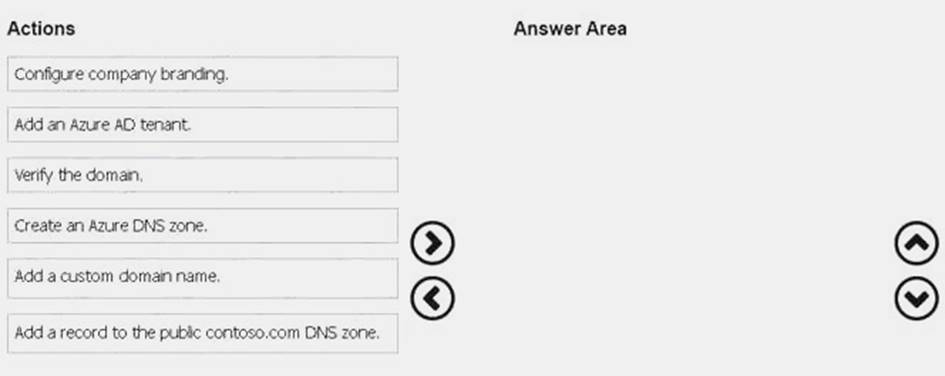
Answer:
Explanation: The process is simple:
Add the custom domain name to your directory
Add a DNS entry for the domain name at the domain name registrar Verify the custom domain name in Azure AD
References: https://docs.microsoft.com/en-us/azure/dns/dns-web-sites-custom-domain
NEW QUESTION 20
DRAG DROP
You have an on-premises network that includes a Microsoft SQL Server instance named SQL1. You create an Azure Logic App named App1.
You need to ensure that App1 can query a database on SQL1.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.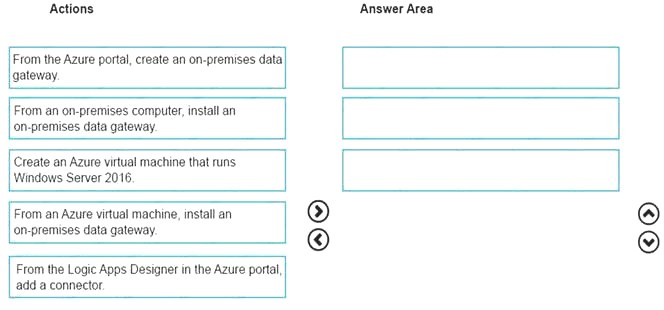
Answer:
Explanation: To access data sources on premises from your logic apps, you can create a data gateway resource in Azure so that your logic apps can use the on-premises connectors.
Box 1: From an on-premises computer, install an on-premises data gateway.
Before you can connect to on-premises data sources from Azure Logic Apps, download and install the on-premises data gateway on a local computer.
Box 2: From the Azure portal, create an on-premises data gateway Create Azure resource for gateway
After you install the gateway on a local computer, you can then create an Azure resource for your gateway. This step also associates your gateway resource with your Azure subscription.
Sign in to the Azure portal. Make sure you use the same Azure work or school email address used to install the gateway.
On the main Azure menu, select Create a resource > Integration > On-premises data gateway.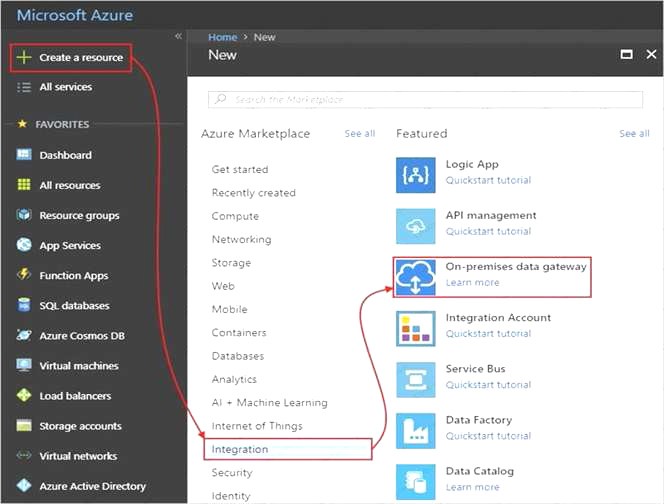
On the Create connection gateway page, provide this information for your gateway resource.
To add the gateway resource to your Azure dashboard, select Pin to dashboard. When you're done, choose Create.
Box 3: From the Logic Apps Designer in the Azure portal, add a connector
After you create your gateway resource and associate your Azure subscription with this resource, you can now create a connection between your logic app and your on-premises data source by using the gateway.
In the Azure portal, create or open your logic app in the Logic App Designer. Add a connector that supports on-premises connections, for example, SQL Server. Set up your connection.
References:
https://docs.microsoft.com/en-us/azure/logic-apps/logic-apps-gateway-connection
P.S. Easily pass AZ-102 Exam with 195 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy AZ-102 Dumps: https://www.2passeasy.com/dumps/AZ-102/ (195 New Questions)